Behavior (based on sandbox results):
Xubuntu Website Hacked: “Safe Downloader” Trojan Masqueraded as Official Installer
How it started :
A disturbing
security incident has surfaced,
The official Xubuntu website was briefly compromised, distributing
malware via its download page.
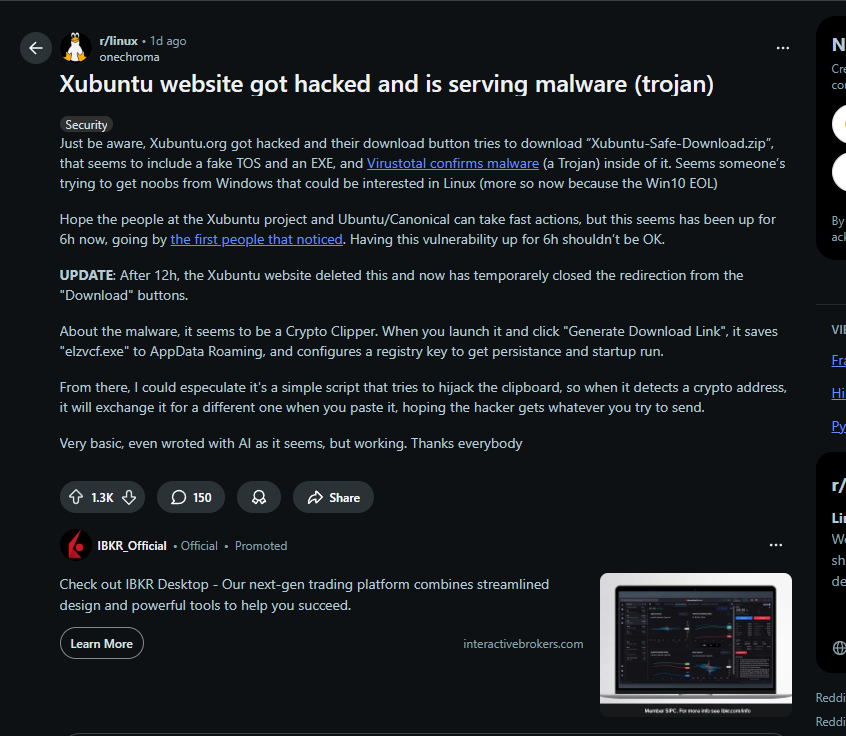
A Reddit user first raised the alarm, claiming the Xubuntu website had been hacked.
-https://www.reddit.com/r/linux/comments/1oad1m6/xubuntu_website_got_hacked_and_is_serving_malware
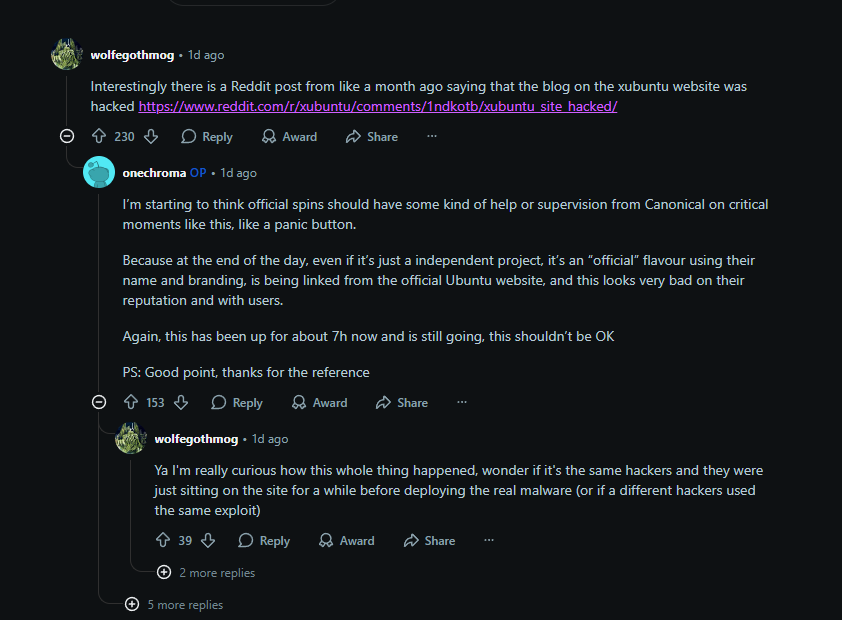
Based on those comments, there is a similar reddit post from a month earlier
(unreliable but interesting)
Which leads to this post:
Which is a clear dead end.
The link doesnt lead to anything, no pic so
info.
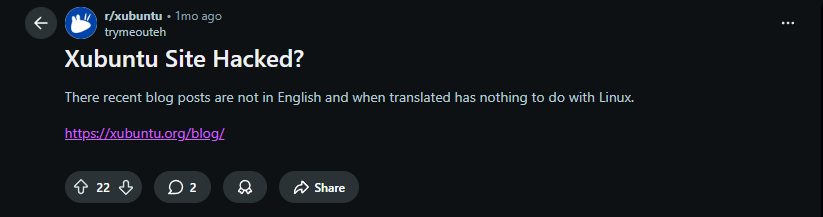
In addition to the reddit thread, a nother claim appeared on ubuntu forums :
-https://discourse.ubuntu.com/t/xubuntu-org-hacked/70074/2
How it works :
During the compromise, clicking the "Download" button allegedly led to a
file named "Xubuntu-Safe-Download.zip."
This archive contained a Windows executable, which was identified by VirusTotal as a Trojan. This malicious file was designed to look like a legitimate
installer, even including a fake terms-of-service document.
The malware, identified as a crypto clipper, was designed to hijack cryptocurrency transactions. It would operate by replacing wallet addresses copied to a user's clipboard with the attacker's own addresses.
The malicious redirection was reportedly active for about six hours before the Xubuntu team removed the compromised link. Currently, the "Download" link on the website simply redirects back to the homepage, which suggests the team is aware of the issue and has taken action.
As of now, neither the Xubuntu project nor Canonical has released an official statement to confirm or deny the breach, and the method of attack remains unknown. Users are advised to await an official update before drawing conclusions. The incident has also been raised on the Ubuntu Discourse forums, but the thread is currently locked for staff review.
Summary (TL;DR)
The official Xubuntu website was compromised, leading to the distribution of a malicious Windows executable named Xubuntu-Safe-Downloader.exe.
|
Detail |
Status |
|
Date and scope of compromise |
Compromise detected Oct 18–19, 2025. Scope limited to download page redirection. |
|
File name |
Xubuntu-Safe-Downloader.exe |
|
Attack vector |
Modified download page delivered a malicious .zip archive via a replacement torrent/mirror link. |
|
Affected users |
Primarily Windows users attempting to download Xubuntu via the compromised link. |
Timeline
A concise overview of the incident's progression:
|
Date |
Event |
|
Oct 18–19, 2025 |
Compromise detected internally. |
|
Oct 19, 2025 |
Redit\ubunto posts |
|
Oct 19, 2025 |
Xubuntu team confirms the issue and pulls the main website offline. |
|
Oct 20, 2025 |
News outlets (CyberNews, OMGUbuntu) publish findings. |
|
Oct 21+, 2025 |
Xubuntu team announces site rebuild and migration to a static architecture. |
Technical facts
The malicious payload was a Windows-targeting trojan, deliberately packaged to exploit users seeking the Linux distribution:
- Malicious file: Xubuntu-Safe-Downloader.exe
- Distribution method: Replaced the legitimate torrent download link on the official website.
Behavior (based on sandbox results):
- Clipboard hijacker: The primary function is a clipboard hijacker, specifically targeting cryptocurrency addresses in memory to redirect funds during transactions.
- Spoof GUI: Displays a fake installer interface with the text “Target OS: Xubuntu” to appear legitimate during execution.
- Outbound connections: The executable attempts outbound connections, likely for Command and Control (C2) communication, though the C2 server identity remains unconfirmed.
Official response
The Xubuntu project team released official statements regarding the scope and path forward:
- Integrity Confirmation: The team stated unequivocally, “No ISO images were affected.” The compromise was limited to the front-facing website infrastructure.
- Rebuild Plan: The entire website is slated to be rebuilt and secured as a static site to minimize future server-side execution risks.
- User Advisory: Users were strongly urged to verify file hashes before executing downloads and to strictly avoid third-party or unofficial mirrors.
Strategic commentary (GreatBinary)
This compromise is a classic illustration of supply chain risk targeting trust in brand, not code.
Attackers exploited a vulnerability in a single point of web infrastructure, effectively bypassing the Xubuntu project's established security protocols. For the end-user, this meant that trust was compromised at the point of installation, rendering the integrity of the core code irrelevant to the initial victim. The incident serves as a stark warning about the paramount importance of stringent security hygiene across all public-facing assets of open-source projects.
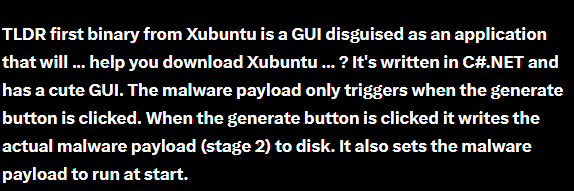
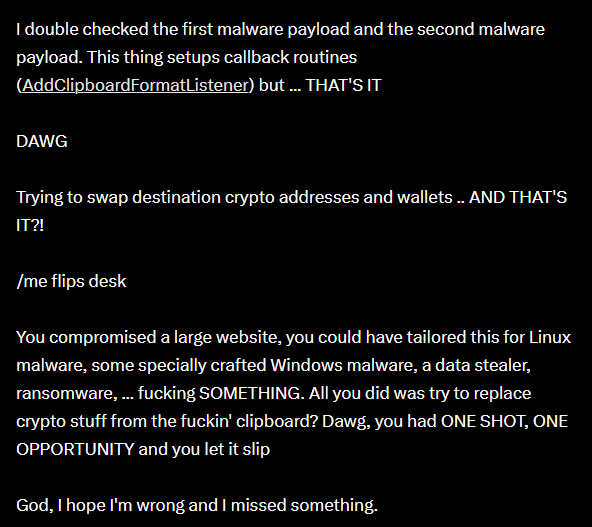
Regarding the malware itself, if we are to credit the assessment by "smelly" from VX-underground which I personally do, the complexity of the payload appears to be minimal. As per his post (link: https://x.com/vxunderground/status/1979885711579865307):
The analysis suggests the malware's sole function is to alter cryptocurrency
addresses in the clipboard, tricking users into inadvertently sending funds to the attacker. While I plan to personally examine the malware, initial findings
align with observations that the chosen attack vector is unusually simple and perhaps unsophisticated given
the ability to achieve mass delivery. The attack
targets cryptocurrency users but is distributed through a non-crypto-focused channel. Furthermore, there has been no attempt to hide or obfuscate the
malware from a technologically savvy community, a curious omission for this type of operation.
References
Source: cybernews.com/security/xubuntu-site-compromise-hackers-peddle-malware
Source: omgubuntu.co.uk/2025/10/xubuntu-website-malware-hack
Source: github.com/xubuntu
Source:https://linuxiac.com/user-flags-possible-malware-incident-on-xubuntu-org/
Source:https://x.com/vxunderground/status/1979885711579865307