Microsoft365 Breach Exposes38 Million Records
Microsoft has confirmed a significant data breach within its Microsoft 365 platform, exposing the records of approximately 38 million users. The incident, disclosed by the Microsoft Security Response Center on Monday, was attributed to a misconfigured Azure cloud storage container that was inadvertently left open to the public for six weeks before being discovered.
The breach was identified during a routine internal security audit. While full payment details and passwords were not exposed, the leaked data includes a sensitive mix of personal and account information:
- Personal Information:
- Names
- Email addresses
- Phone numbers
- Dates of birth
- Residential addresses
- Account Information:
- User IDs
- Subscription types
- Account creation dates
- Service usage data
- Device information
In a statement, Microsoft confirmed it took immediate action to secure the exposed data container upon discovery. "We have secured the misconfigured endpoint and are implementing additional security measures across our cloud infrastructure," the company stated. "All affected customers are being notified directly about this event."
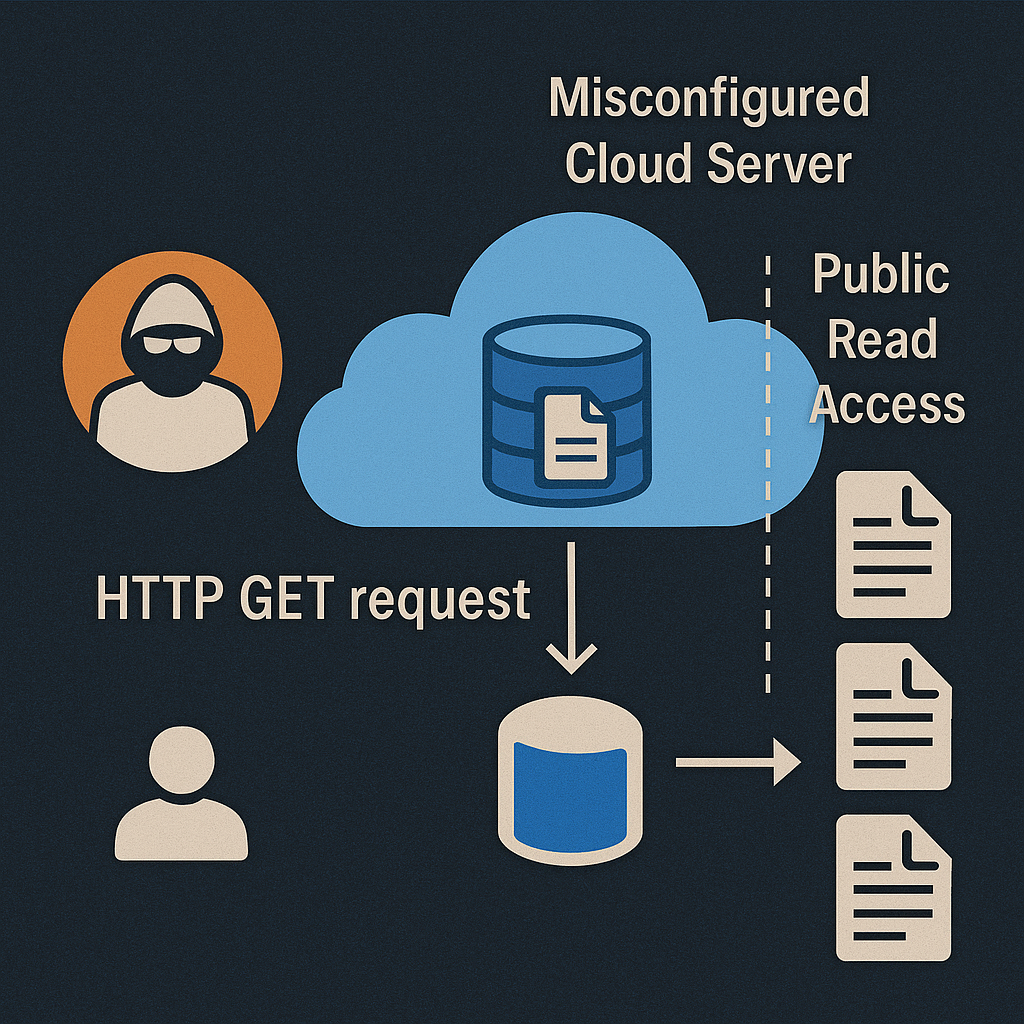
The root cause of the breach stems from a fundamental yet persistent issue in cloud security: misconfiguration of access controls. In this case, an Azure Blob Storage container-used to store unstructured data such as logs, backups, and user information - was inadvertently configured with public read permissions. This setting effectively bypassed Azure’s default security model, allowing anonymous HTTP GET requests to retrieve stored objects without requiring authentication or a valid Azure AD token.
When a blob container is set to “public,” its contents can be indexed or directly accessed if the container’s URL structure is known or guessed, often taking the form:
https://<account>.blob.core.windows.net/<container>/<filename>
Such URLs are frequently discovered by automated scanners, search engine crawlers, or even malicious reconnaissance tools designed to identify open cloud buckets across providers.
In secure configurations, Azure Role-Based Access Control (RBAC) and Shared Access Signatures (SAS) tokens are used to tightly restrict access, enforcing time-limited, scoped permissions. However, in this instance, the misconfiguration bypassed these mechanisms, leaving sensitive metadata and user records exposed.
This incident underscores how even a single incorrect ACL (Access Control List) or public access flag in a cloud resource can lead to mass data exposure, despite underlying encryption or network segmentation controls remaining intact.
What Microsoft 365 Users Should Do Now
Microsoft has stated that it has secured the misconfigured container and is notifying affected users directly. The company also emphasized that it is taking additional steps to enhance its cloud security protocols and prevent similar incidents in the future.
Given the recent Microsoft 365 breach, which exposed 38 million user records due to a misconfigured cloud server, users are strongly advised to take immediate precautionary measures. This incident highlights the ongoing vulnerability even of major technology companies to configuration errors, emphasizing the vital need for continuous automated security scanning and stringent access controls in cloud environments.
Microsoft has issued the following recommendations for all users:
- Monitor Your Account: Regularly check your Microsoft 365 account for any unusual activity or unrecognized logins.
- Enable Multi-Factor Authentication (MFA): Implement MFA without delay, as it adds a critical second layer of security to your account.
- Exercise Caution with Phishing: Be highly skeptical of unsolicited emails, especially those requesting personal information, as scammers may use leaked data to create convincing phishing attempts.
- Change Your Password: As a general security measure, it is advisable to change your Microsoft account password.
For further details, please refer to the official statement from the Microsoft Security Response Center. Users should also remain vigilant against phishing and monitor their accounts for any suspicious activity.