From Mapping Tool to Malicious Web Shell
Hiding in Plain Sight: Chinese Hackers Weaponize Mapping Software in Year-Long Spy Campaign
A sophisticated Chinese state-sponsored hacking group known as Flax Typhoon has been discovered living inside victim networks for over a year by turning a popular mapping server into a stealthy and persistent backdoor.
In a detailed report from cybersecurity firm ReliaQuest, researchers have uncovered a long-running cyber-espionage campaign that weaponized a legitimate feature of ArcGIS servers—a widely used platform for geographic information and mapping. The group, also tracked as Ethereal Panda, is believed to be linked to the Beijing-based Integrity Technology Group.
The attack highlights a dangerous and growing trend of "living-off-the-land," where hackers abuse a system's own trusted tools to avoid detection.
From Mapping Tool to Malicious Web Shell
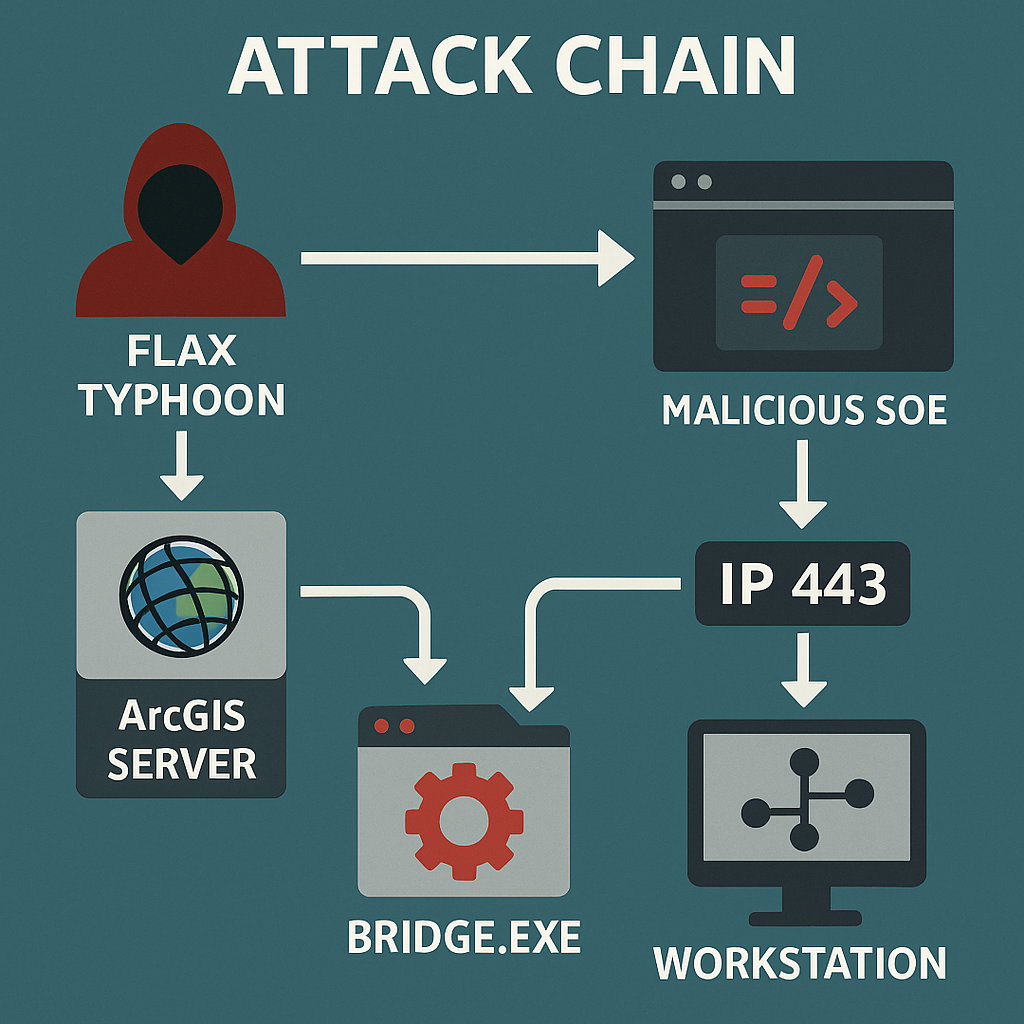
The core of the operation was an "unusually clever attack chain." After compromising an administrator account on a public-facing ArcGIS server, Flax Typhoon didn't install obvious malware. Instead, they deployed a malicious Server Object Extension (SOE)—a type of plugin for ArcGIS—which functioned as a hidden web shell.
"The attackers activated the malicious SOE using a standard ArcGIS extension... making their activity difficult to spot," ReliaQuest said. To maintain exclusive control, the hackers protected their backdoor with a hard-coded key, locking out other attackers and even curious system administrators.
A Backdoor Built to Last
Flax Typhoon's methods for persistence were particularly advanced. To ensure their access survived reboots and even system restores, they:
- Dropped a Disguised VPN: A renamed VPN executable, bridge.exe, was placed in the core System32 folder.
- Created an Auto-Start Service: A new Windows service named "SysBridge" was created to automatically launch their VPN tool every time the server was restarted.
- Embedded in Backups: In a truly sophisticated move, the malicious component was embedded within system backups, allowing the backdoor to be reinstated even after a full system recovery.
The bridge.exe tool would establish an outbound connection to an attacker-controlled server on port 443, the standard for secure HTTPS traffic. This made the malicious communication blend in with normal network activity.
"This VPN bridge allows the attackers to extend the target's local network to a remote location, making it appear as if the attacker is part of the internal network," explained researchers Alexa Feminella and James Xiang. This effectively allowed them to bypass firewalls and network monitoring.
Once inside, the attackers moved laterally, targeting workstations belonging to IT personnel to steal more credentials and gain deeper control, eventually gaining the ability to reset administrative passwords.
The New Era of Cyber Threats
This incident serves as a stark warning for organizations everywhere. The era of just scanning for malicious files is over. Modern threats are increasingly focused on abusing trusted functionalities.
"This attack highlights not just the creativity and sophistication of attackers but also the danger of trusted system functionality being weaponized," the researchers noted.
"It's about recognizing how legitimate tools and processes can be manipulated and turned against you."
Key Indicators of Compromise (IOCs) from ReliaQuest
C2 IP Addresses:
- 172.86.117[.]230
- 172.86.113[.]142 (also observed in ReliaQuest figures)
Filenames / Artifacts:
- bridge.exe - Renamed SoftEther VPN bridge, found in C:\Windows\System32.
- vpn_bridge.config - SoftEther VPN configuration file.
- hamcore.se2 - SoftEther installation file.
- simplerestsoe.soe - Malicious SOE module (web-shell SOE).
File Hashes (as reported):
- bridge.exe: 4f9d9a6cba88832fcb7cfb845472b63ff15cb9b417f4f02cb8086552c19ceffc
- vpn_bridge.config: 8282c5a177790422769b58b60704957286edb63a53a49a8f95cfa1accf53c861
- hamcore.se2: 84959fe39d655a9426b58b4d8c5ec1e038af932461ca85916d7adeed299de1b3
- simplerestsoe.soe: cec625f70d2816c85b1c6b3b449e4a84a5da432b75a99e9efa9acd6b9870b336
High-Priority Hunt and Detection Fingerprints
- Process Monitoring: Look for processes launched from C:\Windows\System32\bridge.exe or services named SysBridge. Actors created a service for VPN binary persistence.
- Outbound HTTPS Alerts: Alert on outbound HTTPS traffic to the listed C2 IPs, especially from ArcGIS-related servers or those running ArcGIS services.
- File Integrity Checks: Search file stores, backups, and ArcGIS SOE directories for simplerestsoe.soe or any SOE differing from vendor-supplied checksums. The SOE was found embedded in backups.
- SoftEther Artifacts: The presence of hamcore.se2 or vpn_bridge.config in unusual locations on servers is highly suspicious.
- Credential Dumping Indicators: Look for activities like the creation/access of pass.txt.lnk, SAM exports, RemoteRegistry enabling, or LSA secret reads, which indicate credential access.